When people talk about controlling AI systems, the conversation often centers on agents: what they can do, which tools they can call, and how to keep them within policy. That focus makes sense, but it is also incomplete.
In production systems, the most important question is not “What is the agent allowed to do?” It is “What is allowed to execute at all?” AI agents are only one execution surface among many.
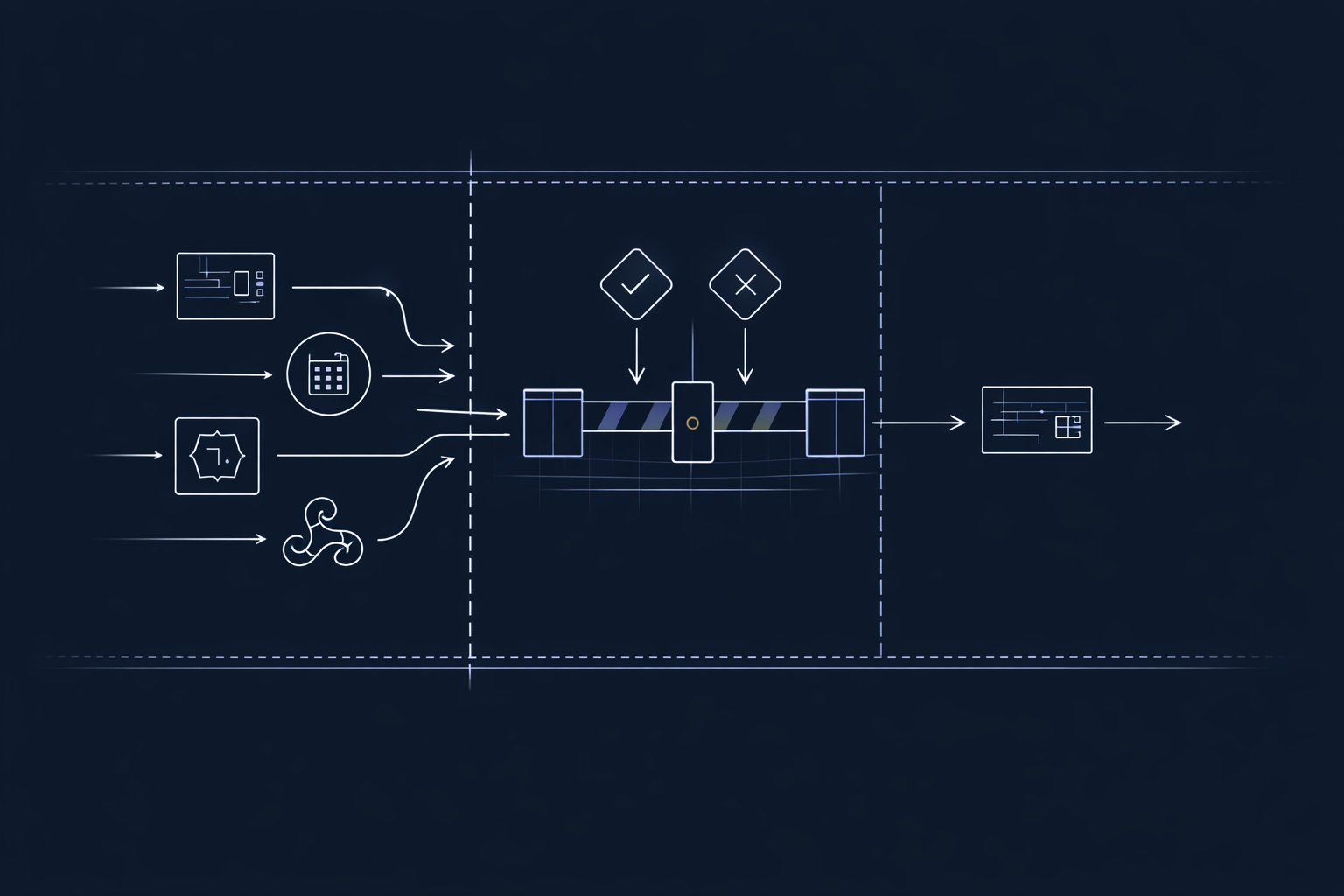
If you want dependable control, you need a consistent enforcement model that applies across the entire runtime footprint: agents, workers, scheduled jobs, event consumers, webhook processors, and any other component that can perform actions.
Start With the Right Unit of Control
Execution control becomes tractable when you use the correct unit. In practice, the most useful unit is an execution surface: any process, instance, or runtime component that can perform work.
Examples include:
- An agent process running on a server or container
- A background worker consuming a queue
- A scheduled task running every N minutes
- An event consumer processing stream events
- A webhook handler executing business logic
- An edge function performing API-side work
These are the places where execution actually happens. If you can gate these surfaces consistently, you can control the system as a whole.
Orchestration Is Not Control
Frameworks and orchestration layers are valuable for structuring work: planning, tool selection, state transitions, and recovery behavior. However, orchestration does not guarantee enforcement.
Orchestration answers:
- What should run next?
- Which tool should be called?
- What state should be persisted?
Enforcement answers:
- Is this allowed to run at all?
- Is this runtime instance permitted right now?
- Can this system start or continue execution?
A system can be perfectly orchestrated and still be uncontrolled if it lacks an external, enforceable gate at startup and at critical runtime boundaries.
The Same Invariant Applies Everywhere
A consistent enforcement model is simple:
- Register the execution surface
- Validate permission at startup
- Proceed only if validation succeeds
This is the same invariant described in Register. Validate. Work. The difference here is scope: the invariant is not agent-specific. It applies to every surface that can execute.
Execution Surfaces You Should Gate
1) Agent Instances
Agent instances are the obvious surface. Whether you run one agent or many, each instance should validate at startup. If it is not allowed, it must not begin work.
This is how “swarm growth” becomes enforceable: additional instances are blocked at startup rather than relying on internal coordination.
2) Background Workers
Most AI-enabled systems include workers: queue processors, ingestion jobs, indexing tasks, enrichment pipelines, or action dispatchers.
These components often have broad permissions and operate continuously. If they start without validation, they can continue doing work long after authorization should have been withdrawn.
Treat each worker instance as an execution surface. Validate before consuming work. If validation fails, the worker should not pull tasks.
3) Scheduled Jobs
Cron-style jobs and scheduled tasks are frequently overlooked. They restart automatically, run unattended, and can be triggered across environments.
Gating scheduled jobs is straightforward: validate at startup of the job invocation. If validation fails, exit immediately.
4) Event Consumers
Event-driven systems (streams, pub/sub, webhooks, internal events) create execution surfaces that are easy to scale and hard to control without explicit gating.
Each consumer instance should validate before processing events. If authorization is removed, consumers should stop consuming.
5) Webhook and Action Handlers
Webhook handlers and action endpoints are execution surfaces that frequently trigger downstream effects: purchases, notifications, database writes, external API calls.
These are not “agents,” but they are still execution surfaces. Gating them ensures that systems cannot perform actions unless explicitly permitted.
Why “Device” Is a Useful Abstraction
In practice, execution surfaces map cleanly to device-like identities: independent instances that can be registered, validated, revoked, and audited.
When each execution surface is treated as a device:
- Limits become concrete (growth is blocked at startup)
- Revocation becomes immediate (execution loses permission)
- Auditing becomes consistent (who ran, when, and why)
- Control becomes external (authority lives outside the process)
This abstraction is especially effective for AI systems because execution footprints tend to expand: additional workers, more agent replicas, new event processors, and distributed runtimes.
Putting It Together
If you only gate “agents,” you are likely to miss a large portion of the system that still executes actions. The practical way to achieve real control is to gate execution surfaces everywhere they exist.
The enforcement model does not need to change. What changes is your scope: treat any component that can perform work as an execution surface that must register and validate before it runs.
MachineID implements device-level enforcement for AI agents and execution systems, enabling the same invariant to apply across agents, workers, jobs, and event-driven components.